Rust string data-types
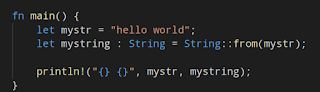
The two first main objects are "str" and String, lets check also the constructors.Imports and functions
Even such a basic program links several libraries and occupy 2,568Kb, it's really not using the imports and expots the runtime functions even the main.
Even a simple string operation needs 544 functions on rust:
Main function
If you expected see a clear main function I regret to say that rust doesn't seem a real low-level language In spite of having a full control of the memory.Ghidra turns crazy when tries to do the recursive parsing of the rust code, and finally we have the libc _start function, the endless loop after main is the way Ghidra decompiles the HLT instruction.
If we jump to main, we see a function call, the first parameter is rust_main as I named it below:
If we search "hello world" on the Defined Strings sections, matches at the end of a large string
After doing "clear code bytes" we can see the string and the reference:
We can see that the literal is stored in an non null terminated string, or most likely an array of bytes. we have a bunch of byte arrays and pointed from the code to the beginning.
Let's follow the ref. [ctrl]+[shift]+[f] and we got the references that points to the rust main function.
After several naming thanks to the Ghidra comments that identify the rust runtime functions, the rust main looks more understandable.
See below the ref to "hello world" that is passed to the string allocated hard-coding the size, because is non-null terminated string and there is no way to size this, this also helps to the rust performance, and avoid the c/c++ problems when you forgot the write the null byte for example miscalculating the size on a memcpy.
Regarding the string object, the allocator internals will reveal the structure in static.
alloc_string function call a function that calls a function that calls a function and so on, so this is the stack (also on static using the Ghidra code comments)
1. _$LT$alloc..string..String$u20$as$u20$core..convert..From$LT$$RF$str$GT$$GT$::from::h752d6ce1f15e4125
2. alloc::str::_$LT$impl$u20$alloc..borrow..ToOwned$u20$for$u20$str$GT$::to_owned::h649c495e0f441934
3. alloc::slice::_$LT$impl$u20$alloc..borrow..ToOwned$u20$for$u20$$u5b$T$u5d$$GT$::to_owned::h1eac45d28
4. alloc::slice::_$LT$impl$u20$$u5b$T$u5d$$GT$::to_vec::h25257986b8057640
5. alloc::slice::hack::to_vec::h37a40daa915357ad
6. core::slice::_$LT$impl$u20$$u5b$T$u5d$$GT$::len::h2af5e6c76291f524
7. alloc::vec::Vec$LT$T$GT$::extend_from_slice::h190290413e8e57a2
8. _$LT$alloc..vec..Vec$LT$T$GT$$u20$as$u20$alloc..vec..SpecExtend$LT$$RF$T$C$core..slice..Iter$LT$T$GT$$GT$$GT$::spec_extend::h451c2f92a49f9caa
...
Well I'm not gonna talk about the performance impact on stack but really to program well reusing code grants the maintainability and its good, and I'm sure that the rust developed had measured that and don't compensate to hardcode directly every constructor.
At this point we have two options, check the rust source code, or try to figure out the string object in dynamic with gdb.
Source code
The string object is defined at string.rs and it's simply an u8 type vector.
And the definition of vector can be found at vec.rs and is composed by a raw vector an the len which is the usize datatype.
The RawVector is a struct that helds the pointer to the null terminated string stored on an Unique object, and also contains the allocation pointer, here raw_vec.rs definition.
The cap field is the capacity of the allocation and a is the allocator:
Finally the Unique object structure contains a pointer to the null terminated string, and also a one byte marker core::marker::PhantomData
Dynamic analysis
The first parameter of the constructor is the interesting one, and in x64 arch is on RDI register, the extrange sequence RDI,RSI,RDX,RCX it sounds like ACDC with a bit of imagination (di-si-d-c)So the RDI parámeter is the pointer to the string object:
So RDI contains the stack address pointer that points the the heap address 0x5578f030.
Remember to disable ASLR to correlate the addresses with Ghidra, there is also a plugin to do the synchronization.
Having symbols we can do:
p mystring
and we get the following structure:
String::String {
vec: alloc::vec::Vec
buf: alloc::raw_vec::RawVec
ptr: core::ptr::unique::Unique
pointer: 0x555555790130 "hello world\000",
_marker: core::marker::PhantomData
},
cap: 11,
a: alloc::alloc::Global
},
len: 11
}
}
If the binary was compiled with symbols we can walk the substructures in this way:
(gdb) p mystring.vec.buf.ptr
$6 = core::ptr::unique::Unique
(gdb) p mystring.vec.len
$8 = 11
If we try to get the pointer of each substructure we would find out that the the pointer is the same:
If we look at this pointer, we have two dwords that are the pointer to the null terminated string, and also 0xb which is the size, this structure is a vector.
The pionter to the c string is 0x555555790130

This seems the c++ string but, let's look a bit deeper:
RawVector
Vector:
(gdb) x/wx 0x7fffffffdf50
0x7fffffffdf50: 0x55790130 -> low dword c string pointer
0x7fffffffdf54: 0x00005555 -> hight dword c string pointer
0x7fffffffdf58: 0x0000000b -> len
0x7fffffffdf5c: 0x00000000
0x7fffffffdf60: 0x0000000b -> low cap (capacity)
0x7fffffffdf64: 0x00000000 -> hight cap
0x7fffffffdf68: 0xf722fe27 -> low a (allocator)
0x7fffffffdf6c: 0x00007fff -> hight a
0x7fffffffdf70: 0x00000005
So in this case the whole object is in stack except the null-terminated string.
More information
- Pentest Tools Review
- Hacking Tools Pc
- Pentest Tools List
- Pentest Tools Download
- Pentest Tools Bluekeep
- How To Install Pentest Tools In Ubuntu
- Nsa Hack Tools Download
- Hacking Tools Hardware
- Free Pentest Tools For Windows
- Bluetooth Hacking Tools Kali
- New Hacker Tools
- Hacking Tools Windows
- Hack Tools For Windows
- Hack Website Online Tool
- Hack App
- Hacking Tools For Windows 7
- Hacker
- How To Hack
- Hacker Tools List
- Hack And Tools
- Hacking Tools Hardware
- Computer Hacker
- Kik Hack Tools
- Hak5 Tools
- Black Hat Hacker Tools
- Hacker Search Tools
- Hacker Tools 2020
- Top Pentest Tools
- Hacking App
- Pentest Tools Port Scanner
- Pentest Automation Tools
- Hack Tools For Ubuntu
- Hacks And Tools
- Github Hacking Tools
- Hack Tools For Games
- Hack Tools For Pc
- How To Install Pentest Tools In Ubuntu
- Hacking Tools Windows 10
- Hacker Tools For Ios
- Nsa Hack Tools Download
- Hacker Tools For Mac
- Hacking Tools For Windows
- Hack Website Online Tool
- Hacker Hardware Tools
- Tools Used For Hacking
- Hacking Tools For Windows 7
- Hack Tools For Games
- Hacking Tools For Games
- Hacker Techniques Tools And Incident Handling
- Pentest Tools Framework
- New Hacker Tools
- Tools For Hacker
- Pentest Tools Port Scanner
- Ethical Hacker Tools
- What Are Hacking Tools
- Hack Tools Online
- Pentest Tools Website
- Hacking Tools 2019
- Hak5 Tools
- Growth Hacker Tools
- Hack Rom Tools
- Physical Pentest Tools
- Hacker Tools For Mac
- Tools 4 Hack
- Hack Tools 2019
- Hack Tool Apk
- Kik Hack Tools
- Hacking App
- Hacker Tools Free
- Pentest Tools For Mac
- Pentest Tools Website
- Pentest Box Tools Download
- Hacker Tools 2019
- Nsa Hack Tools
- How To Install Pentest Tools In Ubuntu
- Hacking Tools Name
- Best Hacking Tools 2019
- Hacking Tools Kit
- Hacker Tools Github
- Underground Hacker Sites
- Hack Tools 2019
- Usb Pentest Tools
- Hack Tools Github
- Hack Tools For Windows
- Hacking Tools
- Pentest Tools Nmap
- Pentest Tools Website
- Pentest Automation Tools
- Pentest Tools Linux
- Hacking Tools And Software
- Hack Website Online Tool
- Hak5 Tools
- Hacker Tools Apk Download
- Hack Tools Online
- Pentest Tools Website
- Bluetooth Hacking Tools Kali
- New Hack Tools
- Hacking Tools Usb
- Hacking Tools Download
- Hacker Search Tools
- How To Make Hacking Tools
- Hacking Tools Windows 10
- Hacking Tools For Windows 7
- Ethical Hacker Tools
- Pentest Tools Android
- Hack Tools Github
- Hacker Tools Free
- Computer Hacker
- Usb Pentest Tools
- Hacking Tools For Kali Linux
- Kik Hack Tools
- Pentest Tools For Ubuntu
- Blackhat Hacker Tools
- Hacking App
- Hacking Tools For Windows
- Hacks And Tools
- Hack And Tools
- Android Hack Tools Github
- Pentest Tools List
- New Hack Tools
- Hacker Tools For Pc
- Hacks And Tools
- Hacking Tools Github
- Pentest Tools Website Vulnerability
- Pentest Tools Windows
- Hack Tools
- Pentest Tools Linux
- Computer Hacker
- Best Hacking Tools 2020
- Pentest Tools Kali Linux
- Wifi Hacker Tools For Windows
- Hacker
- Hak5 Tools
- Hacker Tools Linux
- Pentest Tools Alternative
- Hacking Tools For Games
- Pentest Tools For Ubuntu
- Pentest Tools Find Subdomains
- Github Hacking Tools
- Pentest Tools For Windows
- Hacking Tools For Windows
- Pentest Tools Website
- Hack Tools For Games
- Hacking Tools Pc
- Hack App
- Hackers Toolbox
- Blackhat Hacker Tools
- Hacking Tools For Windows 7
- Usb Pentest Tools
- Hacking Tools For Pc
- Install Pentest Tools Ubuntu
- Pentest Tools For Windows
- Underground Hacker Sites
- Nsa Hack Tools
- Hack Tools Download
















No comments:
Post a Comment